Introduction
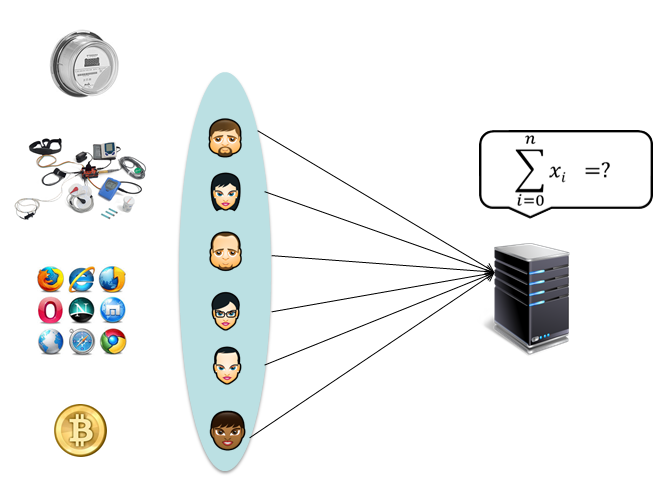
With the advent of networking applications collecting user data on a massive scale, the privacy of individual users appears to be a major concern.
The main challenge is the design of a solution that allows the data analyzer to compute global statistics over the set of individual inputs that are protected by
some confidentiality mechanism. Current approaches suggested a solution that allows a centralized party to compute the sum of encrypted inputs
collected through a smart metering network. The main shortcomings of this solution are its reliance on a trusted dealer for key distribution and the need for key updates
in the case of user joins or leaves. PryTag is a secure protocol for aggregation of time-series data in which the main shortcomings of existing solutions, namely, the requirement for key updates and for the trusted dealer are eliminated.
Efficient and Secure Reachability Computation on Encrypted Location Data
Hanyu Quan, Boyang Wang, Ming Li, Iraklis Leontiadis, and Yuqing Zhang
in submission to TIFS
Collusion Resistant Aggregation from Convertible Tags
Iraklis Leontiadis, Ming Li
International Journal of Information Security (IJIS), pending revision 2016
[pdf]
SecReach: Secure Reachability Computation on Encrypted Location Check-in Data
Hanyu Quan, Boyang Wang, Iraklis Leontiadis, Ming Li and Yuqing Zhang
CANS 2016 Milan, November 2016 [pdf]
PUDA - Privacy and Unforgeability for Data Aggregation
Iraklis Leontiadis, Kaoutar Elkhiyaoui, Melek Onen, Refik Molva
CANS 2015 Marrakesh, Morocco, December 2015 [eprint 2015]
Private and Dynamic Time-Series Data Aggregation with Trust Relaxation
Iraklis Leontiadis, Kaoutar Elkhiyaoui, Refik Molva
CANS 2014 Heraklion, Crete, Greece, October 2014 [slides], [eprint 2014],
Implementation
A research unoptimized prototype implementation of PryTag is set forth.
|
Functionality (sec) \ #Users
|
250
|
500
|
1000
|
10000
|
|
Average Encryption
|
0.123
|
0.123
|
0.122
|
0.125
|
|
Average Auxiliary
|
0.130
|
0.130
|
0.130
|
0.125
|
|
Collector Aggregate
|
0.014
|
0.030
|
0.059
|
0.560
|
|
Aggregator Decryption
|
0.907
|
0.963
|
1.326
|
4.534
|
Practical applications
Smart Metering
User Profiling
Medical Applications
Financial Transactions